Technical String Audit – Ast Hudbillja Edge, caebzhizga154, fhogis930.5z, nop54hiuyokroh, wiotra89.452n Model
A technical string audit of the Ast Hudbillja Edge and related identifiers demands a disciplined, reproducible approach. It frames data models, IDs, and formats against explicit standards, testing for consistency, integrity, and boundary behavior. The method remains skeptical: assume potential misalignment, document irregularities, and traceable steps to isolate faults. The discussion pauses on concrete criteria and verifiable artifacts, inviting further scrutiny into error handling, normalization, and audit trails to sustain accountability. Consider what comes next.
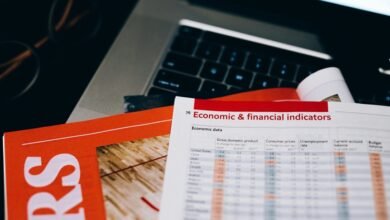
What Is a Technical String Audit and Why It Matters
A technical string audit is a structured assessment of a dataset or sequence of identifiers to verify consistency, integrity, and compliance with predefined standards. It scrutinizes reproducibility, detects subtle anomalies, and chronicles deviations.
Concept drift and schema evolution frame the risk, demanding ongoing validation. The process remains skeptical: findings inform governance, not celebration, ensuring reliable continuity amid changing data ecosystems and evolving specifications.
Auditing Ast Hudbillja Edge and Friends: Data Models, IDs, and Formats
Auditing Ast Hudbillja Edge and Friends involves a disciplined evaluation of data models, identifiers, and formats to ensure consistency and compliance with established standards. The assessment focuses on data models and ids formats, noting potential ambiguities and structural rigidity. Skeptical observers consider error handling clarity and resilience, then evaluate performance implications without bias, emphasizing transparent criteria and disciplined, freedom-centered critique.
Practical Steps: Validation, Error Handling, and Performance Implications
The examination now centers on practical steps for validation, error handling, and performance implications, building on prior assessments of data models and IDs. A disciplined approach employs validation strategies, error containment, and performance profiling, data normalization and schema alignment, type coercion handling and boundary testing. Concise, skeptical assessment emphasizes freedom-minded rigor, avoiding fluff while ensuring robust, measurable safeguards.
Troubleshooting Common Mismatches and Forensic Debugging Tactics
Inconsistent data signals often reveal underlying process gaps, and systematic triage is essential to identify root causes without speculation.
Troubleshooting focuses on reproducible steps, isolated mismatches, and evidence-based conclusions.
Forensic debugging tactics emphasize traceability, versioned artifacts, and audit trails.
Emphasis on data integrity and schema drift clarifies deviations, guiding corrective action while preserving reproducibility, accountability, and freedom to improve systems without blind acceptance.
Conclusion
This audit demonstrates disciplined validation of identifiers and formats, revealing consistent patterns and notable edge cases without overreaching conclusions. The methodology, evidence trails, and reproducible steps enable traceability and accountability while exposing ambiguities and rigidity in the data model. Results underscore that error handling must be explicit and resilient. In short, the process keeps findings grounded and verifiable, like inspecting each cog in a clockwork mechanism to confirm it fits—no loose screws allowed.